Loading...
Cyber Operations Specialist
The civilian and federal jobs that hire Army Cyber Operations Specialists — with real salaries and the resume that gets callbacks.
Every 17C has more options than a Google search will tell you. Below: career paths, BLS salary data, federal GS series, certifications by target career, and how to translate your experience without losing what made you valuable to the Army in the first place.
Free · No credit card · Tailored resume in under 5 minutes
After the Navy I got hired into 6 federal career fields and tech sales, and sat on federal hiring panels along the way. I spent the last 2 years rebuilding everything I learned into BMR, tuned for how AI actually screens resumes today. This is the system I wish I'd had on day one.
Get a free 17C Cyber Operations Specialist sample resume
One page, built in our template, with your military experience translated into civilian terms hiring managers and ATS systems read. Use it as a reference for your own. Drop your email and we'll send you the download link.
Free. We'll also send occasional job-search tips. Unsubscribe anytime.
Military Role Overview
Army Cyber Operations Specialists (17C) conduct offensive and defensive cyberspace operations in support of Army and joint force missions. They are trained to penetrate adversary networks, defend friendly systems, and conduct full-spectrum cyber operations — from vulnerability assessment to exploitation to incident response.
The 17C training pipeline is one of the longest and most rigorous in the Army. After Basic Combat Training, Soldiers attend the Cyber Operations Specialist course at Fort Eisenhower (formerly Fort Gordon), Georgia, which runs approximately 50 weeks. The curriculum covers network defense, offensive cyber operations, malware analysis, digital forensics, and scripting/programming. Many 17Cs hold TS/SCI clearances and operate within organizations like Army Cyber Command (ARCYBER) and United States Cyber Command (USCYBERCOM).
What sets 17Cs apart in the civilian job market is that they have done the work, not just studied it. While many cybersecurity professionals enter the field through academic programs, 17Cs have conducted live cyber operations against real-world targets and defended production networks under actual threat conditions. Combined with a TS/SCI clearance, this makes them among the most sought-after veterans in the tech sector.
I sat on the federal hiring side after the Navy and 17Cs are some of the easiest cleared cyber hires the federal government can make. The 2210 Information Technology Management series, NSA, and Cyber Command actively recruit 17Cs out of uniform — the offensive cyber experience is genuinely rare in the civilian workforce. — Brad Tachi, Navy Diver veteran & BMR founder
Pay Reality Check
The number that matters when you're deciding what's next: how does civilian pay compare to what you make now?
Military comp is approximate (varies by location/dependents). Civilian is BLS median. Federal includes locality pay. Your real number depends on duty station, family status, GS step, and overtime.
Private Sector Career Paths
Cybersecurity is one of the fastest-growing career fields in the civilian economy, and 17Cs are positioned at the top of the candidate pool. According to the Bureau of Labor Statistics (May 2024), the median annual wage for information security analysts is $120,360 (O*NET 15-1212.00), with employment projected to grow 33% — much faster than average. The demand far exceeds the supply of qualified professionals.
17Cs can pursue multiple tracks within cybersecurity: penetration testing, incident response, threat intelligence, security engineering, and security operations center (SOC) management. The offensive cyber skills are particularly rare and command premium compensation — BLS data shows the broad median, but specialized roles in red teaming and exploit development frequently exceed this significantly in private sector markets.
The TS/SCI clearance alone creates a separate job market. Defense contractors and intelligence community contractors actively recruit cleared cyber professionals, and the clearance premium adds substantial value above uncleared positions.
Civilian Job Title Translations
| Civilian Job Title | Industry | BLS Median Salary | Outlook | Match |
|---|---|---|---|---|
Information Security Analyst O*NET: 15-1212.00 | Technology / Defense / Finance | $120,360 | Much faster than average (33%) | strong |
Penetration Tester / Ethical Hacker O*NET: 15-1212.00 | Technology / Consulting / Defense | $120,360 | Much faster than average (33%) | strong |
Computer Systems Analyst O*NET: 15-1211.00 | Technology / Finance / Government | $103,800 | About as fast as average (10%) | moderate |
Network and Computer Systems Administrator O*NET: 15-1244.00 | Technology / Government | $94,720 | About as fast as average (2%) | moderate |
Database Administrator O*NET: 15-1242.00 | Technology / Finance / Healthcare | $105,060 | About as fast as average (8%) | moderate |
Computer and Information Systems Manager O*NET: 11-3021.00 | Technology / Multiple Industries | $169,510 | Faster than average (17%) | emerging |
Software Developer O*NET: 15-1252.00 | Technology / Defense | $132,270 | Much faster than average (17%) | moderate |
Computer Forensics Analyst O*NET: 15-1212.00 | Law Enforcement / Consulting / Defense | $120,360 | Much faster than average (33%) | strong |
Companies That Hire This Background
See a salary you want? Build a resume targeting it.
BMR rewrites your 17C experience for any of the civilian roles above — keywords, achievements, and language hiring managers actually scan for.
Free · No credit card · 2 tailored resumes included
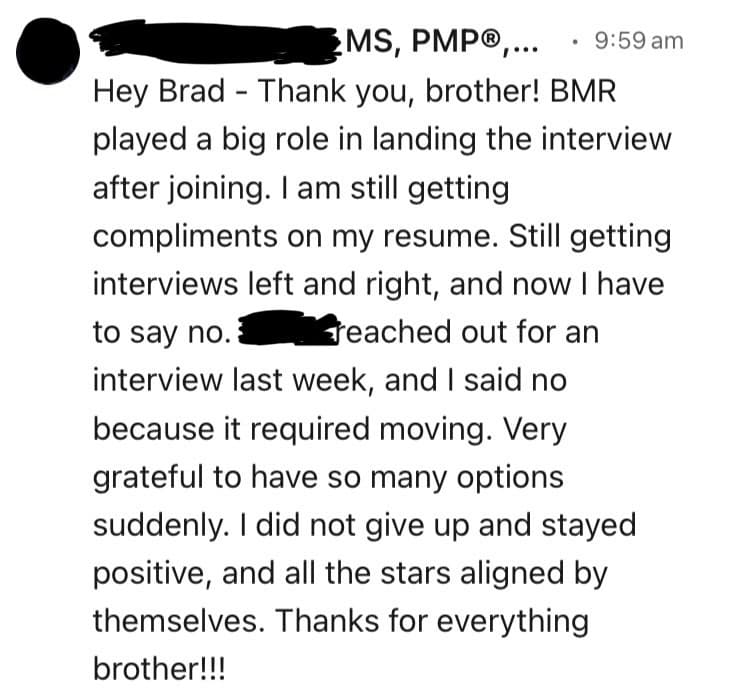
“I am still getting compliments on my resume. Still getting interviews left and right, and now I have to say no. Very grateful to have so many options suddenly.”
Federal Career Paths
The federal government is the largest employer of cybersecurity professionals in the country, and 17Cs have a direct path into multiple agencies. The GS-2210 (Information Technology Management) series is the primary classification, but cyber professionals work across multiple series depending on the agency and role.
NSA, CIA, DIA, and the intelligence community civilian workforce hire 17Cs through direct hire authority — often bypassing the normal competitive hiring process. USCYBERCOM civilian positions provide continuity for Soldiers who want to keep doing the same work without the uniform. DHS/CISA (Cybersecurity and Infrastructure Security Agency) is expanding rapidly and actively recruits veterans with operational cyber experience.
Federal cyber positions use the GS pay scale but some agencies (NSA, DHS/CISA) offer special salary rates and cyber incentive pay that exceed standard GS rates. The Cyber Excepted Service (CES) within DOD uses a separate pay structure specifically designed to compete with private sector cyber salaries.
GS Series & Position Matches
| GS Series | Federal Job Title | Typical Grades | Match | Explore |
|---|---|---|---|---|
| GS-0132 | Intelligence | GS-9, GS-11, GS-12 | View Details → | |
| GS-2210 | Information Technology Management | GS-9, GS-11, GS-12, GS-13 | View Details → | |
| GS-0340 | Program Management | GS-11, GS-12, GS-13 | View Details → | |
| GS-0341 | Administrative Officer | GS-9, GS-11 | View Details → | |
| GS-0080 | Security Administration | GS-7, GS-9, GS-11 | View Details → | |
| GS-1550 | Computer Science | GS-11, GS-12, GS-13 | View Details → | |
| GS-1801 | General Inspection, Investigation, Enforcement | GS-7, GS-9, GS-11 | View Details → | |
| GS-1811 | Criminal Investigator | GS-7, GS-9, GS-11, GS-12 | View Details → | |
| GS-0343 | Management and Program Analyst | GS-9, GS-11, GS-12 | View Details → | |
| GS-0301 | Miscellaneous Administration and Program | GS-9, GS-11, GS-12 | View Details → |
Federal resumes follow different rules. We know them.
Federal hiring uses keyword-matching and structured experience. BMR builds federal-format resumes (USAJobs-ready) with the right keywords, hours/week, and supervisor info — for any GS series above.
Free · No credit card · Federal + civilian resume formats included
Want to Change Careers Entirely?
Not everyone wants to stay in a related field. These career paths leverage your transferable skills — leadership, risk management, logistics, project planning — in completely different industries.
Software Developer
17Cs write scripts, develop tools, and automate processes as part of their core job. The transition from exploit development and automation scripting to software engineering is more about expanding scope than learning new fundamentals.
Data Scientist
Cyber operations involve analyzing massive datasets to find anomalies, patterns, and indicators of compromise. This is data science applied to security. The analytical methodology transfers directly to business intelligence, fraud detection, and predictive analytics.
Cloud Solutions Architect
17Cs understand network architecture, security controls, and infrastructure at a deep level. Cloud architecture is these same concepts applied to AWS, Azure, or GCP environments. The security mindset is increasingly critical as organizations migrate to the cloud.
Management Analyst
Senior 17Cs assess operational readiness, identify vulnerabilities in processes (not just networks), and brief leadership on risk. This is management consulting — analyzing systems, finding problems, and recommending solutions.
Project Management Specialist
Cyber operations require detailed planning, coordination across teams, timeline execution, and risk management. Senior 17Cs who planned and led operations have documented project management experience.
Technical Writer
17Cs write operational plans, after-action reports, vulnerability assessments, and technical procedures. Translating complex technical concepts into clear documentation is something you already do.
IT Compliance Analyst
17Cs understand security controls, compliance frameworks (NIST, RMF), and how to assess whether systems meet requirements. IT compliance and audit roles in finance, healthcare, and government need exactly this skillset.
Pivoting industries? You don't need to start from scratch.
The skills that made you a good Marine, Sailor, Airman, or Soldier transfer further than you think. BMR rewrites your bullets for any of the pivot careers above — without making you sound like you've never done the work.
Free · No credit card · Try unlimited career angles
Skills Translation Guide
If you are applying to cybersecurity positions at defense contractors or government agencies, your terminology likely translates directly — hiring managers in that space know what OCO, DCO, and USCYBERCOM mean. This section is for 17Cs targeting careers outside the defense and intelligence community, where the hiring manager has never held a clearance and thinks "cyber" means IT help desk.
Your operational cyber experience translates into any role involving risk management, technical problem-solving, and complex systems analysis. The key is reframing classified work into unclassified business language without revealing specifics. Focus on methodologies, outcomes, and scale — not tools or targets.
Resume Bullet Examples
Get bullets like these auto-generated for your resume.
BMR turns your 17C duties and accomplishments into civilian bullets that match the job you're applying for — no manual translation, no rewriting.
Free · No credit card · Tailored to each job posting
Certifications by Career Path
Which certifications you need depends on where you're headed. Find your target career path below.
Cloud Computing
Cybersecurity
IT & Networking
Project Management
Got a cert? Don't bury it. List it the right way.
The wrong placement can sink an otherwise strong application. BMR knows where each cert ranks, what to call it, and how to frame it for ATS keyword matching and hiring manager attention.
Free · No credit card · Built around your real certs and clearance
Transition Resources
For Staying in Cybersecurity
SkillBridge Programs: Multiple cybersecurity companies participate in DOD SkillBridge, including Booz Allen Hamilton, SAIC, and ManTech. Check the SkillBridge database for current openings. Start the conversation 12+ months out.
SANS Institute: SANS offers the most respected cybersecurity training in the industry. GIAC certifications from SANS carry significant weight. GI Bill covers many SANS programs — verify current approval status.
Cyber Workforce Framework (NICE): The NICE Framework from NIST maps cybersecurity work roles and competencies. Use this to match your military skills to civilian job descriptions and identify certification gaps.
DEF CON / Black Hat: Industry conferences where hiring happens. Many have veteran-specific networking events. The connections you make here can lead directly to job offers.
For Careers Outside of Cybersecurity
Project Management: The PMP certification (PMI) is the standard for project management careers. Your experience managing cyber operations and teams counts toward the experience requirement.
Cloud Computing: AWS, Azure, and GCP certifications are highly valued. AWS training offers free courses and GI Bill covers many programs. Cloud security is a natural extension of your skills.
Federal Employment (USAJobs): Create your USAJobs profile immediately. Key agencies: NSA, DHS/CISA, FBI, CIA, DIA, USCYBERCOM civilian, and DOD CIO. Federal resumes are 2 pages max. Build yours here.
Veteran Networking: American Corporate Partners (ACP) provides free mentorship from corporate executives. Get paired with someone in tech — completely free for veterans.
Clearance Leverage: A TS/SCI clearance is one of the most valuable assets in the job market. ClearanceJobs.com lists thousands of positions requiring active clearances. Do not let yours lapse.
Education Benefits: Use the GI Bill Comparison Tool to verify program approval. Many cybersecurity bootcamps and degree programs are VA-approved. SANS, CompTIA, and (ISC)2 certifications are frequently covered.
BMR Career Resources
Army Resume Guide: MOS Translation | Complete Military Resume Guide | Army ETS Checklist | Build Your Resume Free
Your 30 / 60 / 90-Day Transition Plan
Most veterans do this backwards — they wait until terminal leave to start, then panic. Here's the actual sequence that works.
Set the foundation
- Pull your DD-214 (request from Milconnect if separated)
- List your top 3 civilian roles AND top 3 GS series
- Build your tailored 17C resume — BMR does it free
- Write 1 strong LinkedIn headline (not "veteran seeking opportunities")
- Pull together your evals/performance reports for accomplishments
Apply with intent
- Apply to 5–10 jobs/week — quality over quantity
- Tailor every resume to the job description (BMR auto-tailors)
- Connect with 5 people/week on LinkedIn (not a spray)
- Set up a USAJobs profile and a saved-search alert for your GS series
- Practice translating your military bullets out loud — explain to a civilian friend
Close the offer
- Track every application — date, status, contact, notes
- Follow up 7–10 days after each application
- Prep for behavioral interviews using the STAR method
- Negotiate salary — don't take the first offer (BLS median is your floor)
- Stay applying even after one offer — leverage = options
Print this. Tape it to your monitor. Veterans who treat the transition like a 90-day op get hired faster than the ones who treat it like an emergency.
Frequently Asked Questions
What is the salary for civilian cybersecurity professionals?
How valuable is my TS/SCI clearance in the civilian market?
What if I want to leave cybersecurity entirely?
Which cybersecurity certifications should I prioritize after separation?
Can I talk about classified work on my resume?
How does Veterans Preference work for federal cybersecurity jobs?
Should I get a computer science degree or focus on certifications?
Is the cybersecurity job market saturated?
Where are the best job markets for cyber veterans?
Can I start job searching while still on active duty?
Translate your 17C Cyber Operations Specialist experience into a resume that gets callbacks
Stop rewriting from scratch every time you apply. BMR turns your military experience into civilian and federal resumes — tailored to each job.